Alisanne Steele | TheSoftwareConsultant | Thursday, August 2, 2018
Verizon recently released its Mobile Security Index report highlighting the difficulty businesses face in balancing convenience and user experience with security concerns and the reality of today’s internet environment that is filled with risk.
The report finds that Companies are sacrificing mobile security for convenience and performance. Companies that said they knew their organization did this were more than twice as likely to have experienced data loss or downtime (45% compared to 19%).

Nearly all respondents (93%) agreed that mobile devices present a serious and growing security threat.
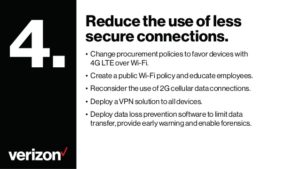
Despite this, many were failing to take basic precautions. Only 39% said they change all default passwords and over half (51%) didn’t have a public Wi-Fi policy. And of the companies that said they do have a policy, 14% said that they use public WiFi despite it being officially prohibited.

Most know they need to take more action. 93% agreed that organizations should take mobile security more seriously.

Where does your firm fall in the Security Index Spectrum, and what can you do to increase your firm’s security and reduce your risk of data loss or exposure?
Employees are one of your greatest points of exposure. Staff training, (Enforced) written policies, and Mobile Device Management solutions can greatly reduce your risk from phishing, ransomware and other common points of exposure.

Enforce strong password policies, craft and employ acceptable use and BYOD policies and invest time in making staff aware of your policies and the importance of adherence.

Review your plan with all your staff annually as it relates to changes in your environment, future IT changes, and current devices and solutions in the market. Develop a procedure for reporting and tracking incidents to provide insight into shoring up your policies in the future.

Prohibit all staff from using public WiFi and other potentially risky sources for internet connections. Update (and replace) all devices regularly to stay within industry standards for best security practices. Provide private mobile internet solutions to staff that frequently access the internet outside of controlled environments.
Enlist the help of seasoned professionals to assist you in the design and implantation of your on-premise, on-line, and mobile security policies, procedures and solutions. If you would like to read or share the full report, it can be accessed here.
As always, we are here to help!
Sanne
Alisanne Steele | TheSoftwareConsultant | Thursday, August 2, 2018

